Inside the
Platform. Built for defenders who are tired of scanner output that reads like a phone book.
Nine capabilities, one platform. From the first scan request to the final executive PDF — this is what your team works with day one.
One pane, every signal.
Tracked exposures, pentest readiness, new exposures in 24h, critical issues open, active exploit risk — at a glance.
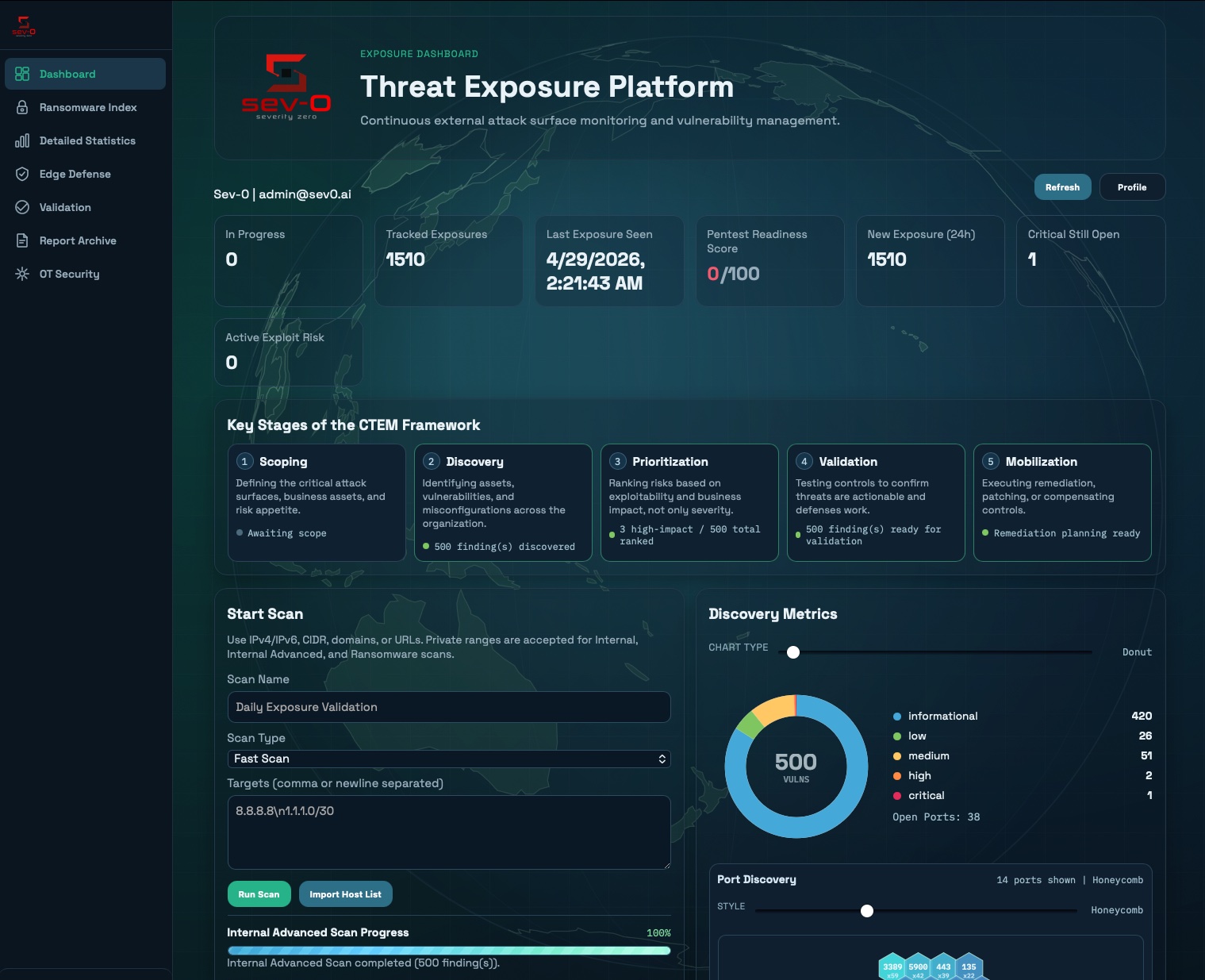
Nine modules, one workflow.
Continuous Multi-Engine Scanning
Seven modes from Fast recon to Ultra masscan-driven sweeps, plus Comprehensive, Advanced, Internal, and looping Continuous assessments. Scheduled daily through annually with duplicate-scope detection and per-tenant admission controls.
Industrial Protocol Coverage
Read-only probes for Modbus, S7comm, EtherNet/IP, BACnet, DNP3, OPC UA, FINS, Fox, CODESYS, SNMP, and more. 30+ vendor OUI fingerprints — Siemens, Rockwell, Schneider, ABB, Honeywell, GE, Omron, WAGO, Moxa.
Ransomware Exposure Index
Weighted score blending CVSS (30%), CISA KEV (20%), ransomware-group association (20%), reachability (15%), asset density (10%), and misconfigurations (5%). Curated knowledge base maps findings to attacker phases.
Internal Edge Scanner
One-command Docker deploy. Encrypted tunnel-bridge means no inbound ports on the client network. Eleven automated readiness checks — connectivity, authenticity, transport, tenant segmentation — verify every node.
Finding Lifecycle Engine
Fingerprint-based dedup across scans. Automatic flagging of net-new exposures, reopened findings, and materially changed evidence. Auto-close on retest. Full state history preserved for audit.
4-Stage Confidence Funnel
Detected → Corroborated → Validated → Exploitability Confirmed. Per-finding re-checks. Session-based workflows seed from any recent scan. Configurable scan-age eligibility (default 15 days) keeps signals fresh.
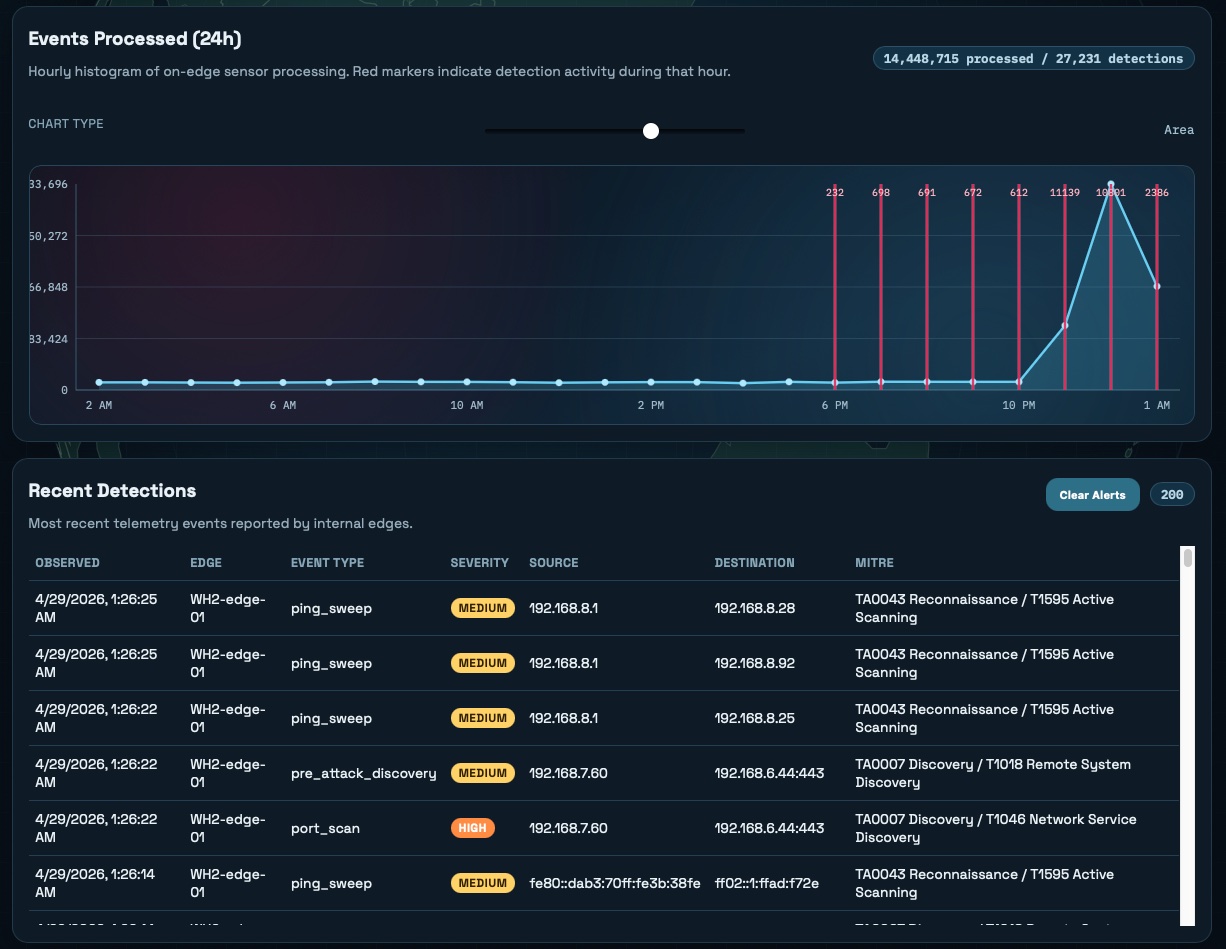
Pre-Attack Sensor
Detects ping sweeps (ICMP, ARP, IPv6 NS), SYN fan-out port scans, Responder-style LLMNR/NBNS/mDNS anomalies, and IPv6 RA spoofing. Mapped to MITRE ATT&CK discovery techniques. Configurable sensitivity, alert suppression.
Pentest-as-a-Service Workflow
Eight-stage engagement lifecycle from Information Needed through Report Available, with client-visible status, scope target management, per-engagement notes, and a full event audit trail.
Executive & Technical Outputs
Per-scan XLSX exports, technical PDFs, executive summaries, JSON evidence packs, scan-target CSVs, and CycloneDX 1.5 SBOMs for OT inventory. Optional local LLM standardizes finding language.
The scanner
becomes a sensor.
The same edge agent that reaches your private networks runs as a passive honeypot — detecting the reconnaissance phase before exploitation begins. Ping sweeps, SYN fan-out scans, Responder-style LLMNR/NBNS anomalies, IPv6 router-advertisement spoofing — all classified, scored, and mapped to MITRE ATT&CK.
- ICMP, ARP, and IPv6 NS host discovery detection
- SYN fan-out and recon-heuristic port scan flags
- LLMNR / NBNS / mDNS response anomaly detection
- Configurable 1–10 sensitivity scale + alert suppression
- Particle-cloud sensor dashboard with hourly histogram

From entry,
to finding.
Automated path candidates trace from internet-facing entry points through internal pivots to the affected host and the rule that fired. Click any node to inspect the underlying evidence — request bodies, response headers, banner data, the full chain.
- Internal Edge Sensor → host → finding rule chain
- Severity color-coding (Critical / High / Medium)
- Filterable by informational findings on/off
- Drill-through to evidence pack
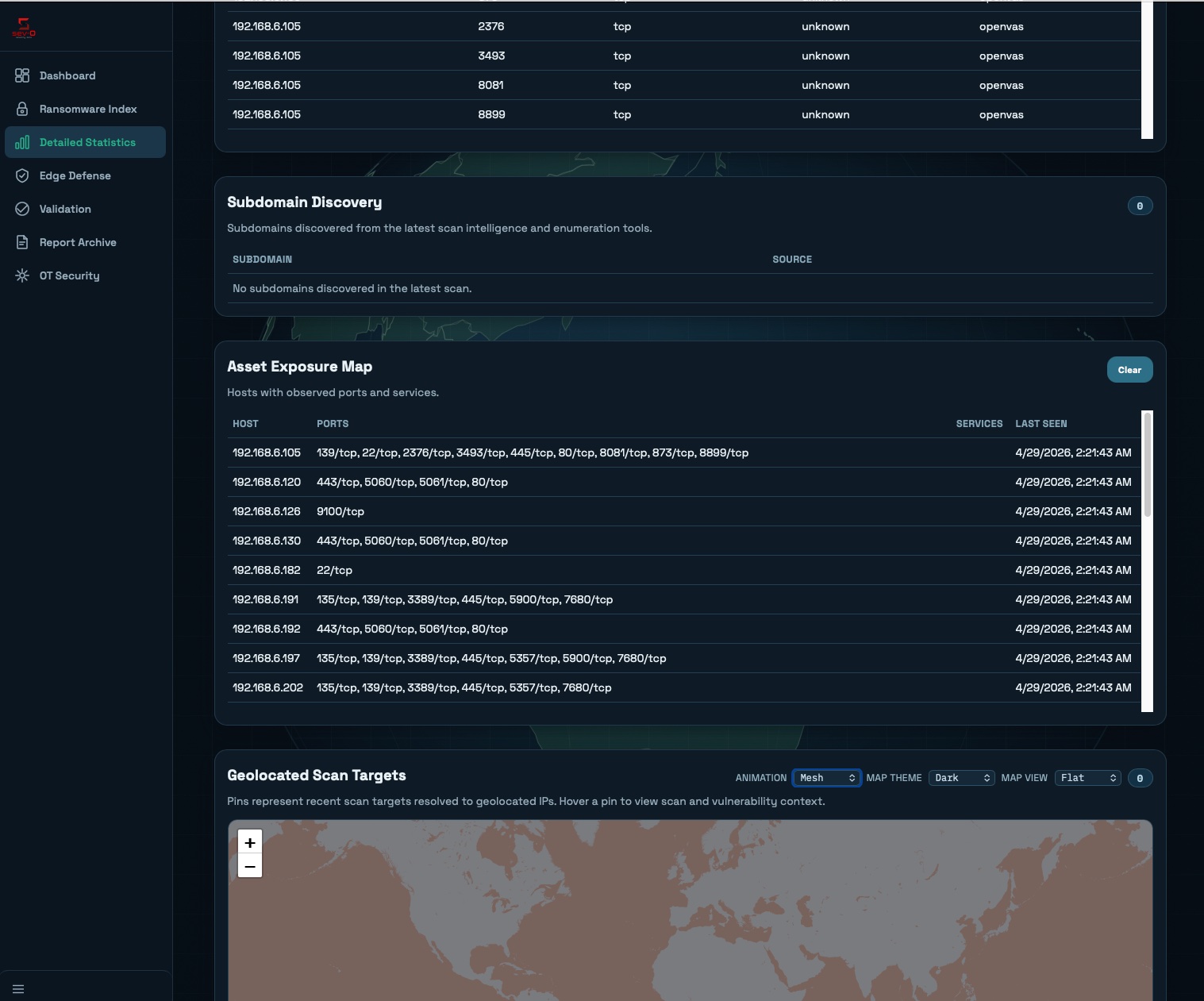
Hosts. Ports.
Geography.
Every host, every observed port, every service banner — with a geolocated map of where your attack surface actually lives. Subdomain discovery, asset exposure mapping, and a global view that updates with every scan.
- Per-host port and service inventory
- Subdomain discovery from intelligence + enumeration
- Geolocated scan target map (mesh, dark, flat themes)
- Last-seen timestamps for change tracking
Stop reacting.
Start hunting exposure.
Book a platform walkthrough — see your real attack surface in under an hour.
