The threats
won't stop.
What are you
doing about it? Detection without action is just a feeling.
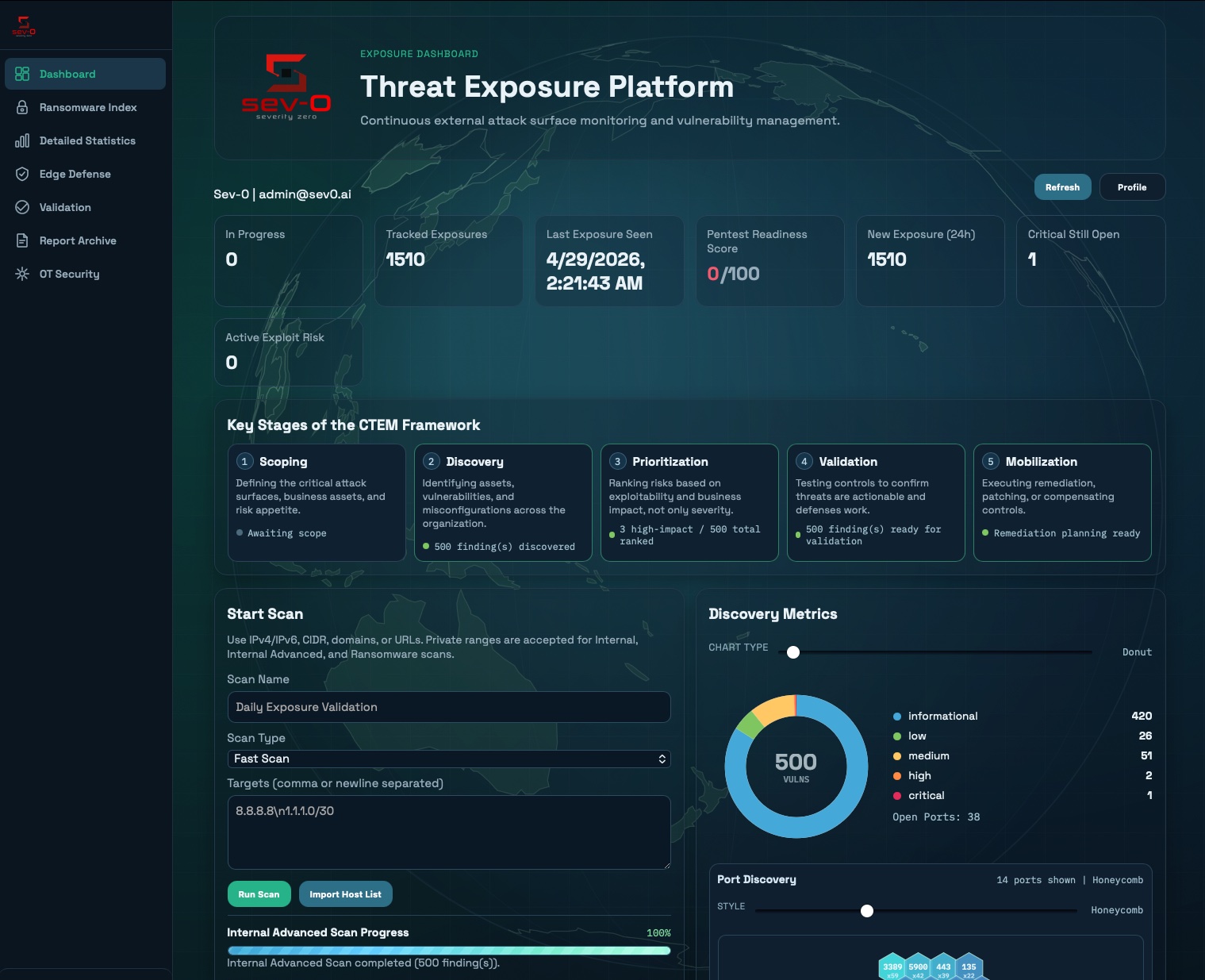
Adversaries don't wait for your quarterly scan. New CVEs land daily. Ransomware crews retool weekly. OT environments expose protocols designed before 'internet' was a word. SeverityZero runs continuously against everything you own — IT, web, cloud, internal, and industrial — then prioritizes what's actually reachable, exploitable, and on a ransomware playbook today.
Fast to Comprehensive
Synced Daily
Read-Only Safe
Detected → Confirmed
What this platform actually does.
Continuous discovery, attacker-priority scoring, pre-breach detection, and proof for everyone who needs it.
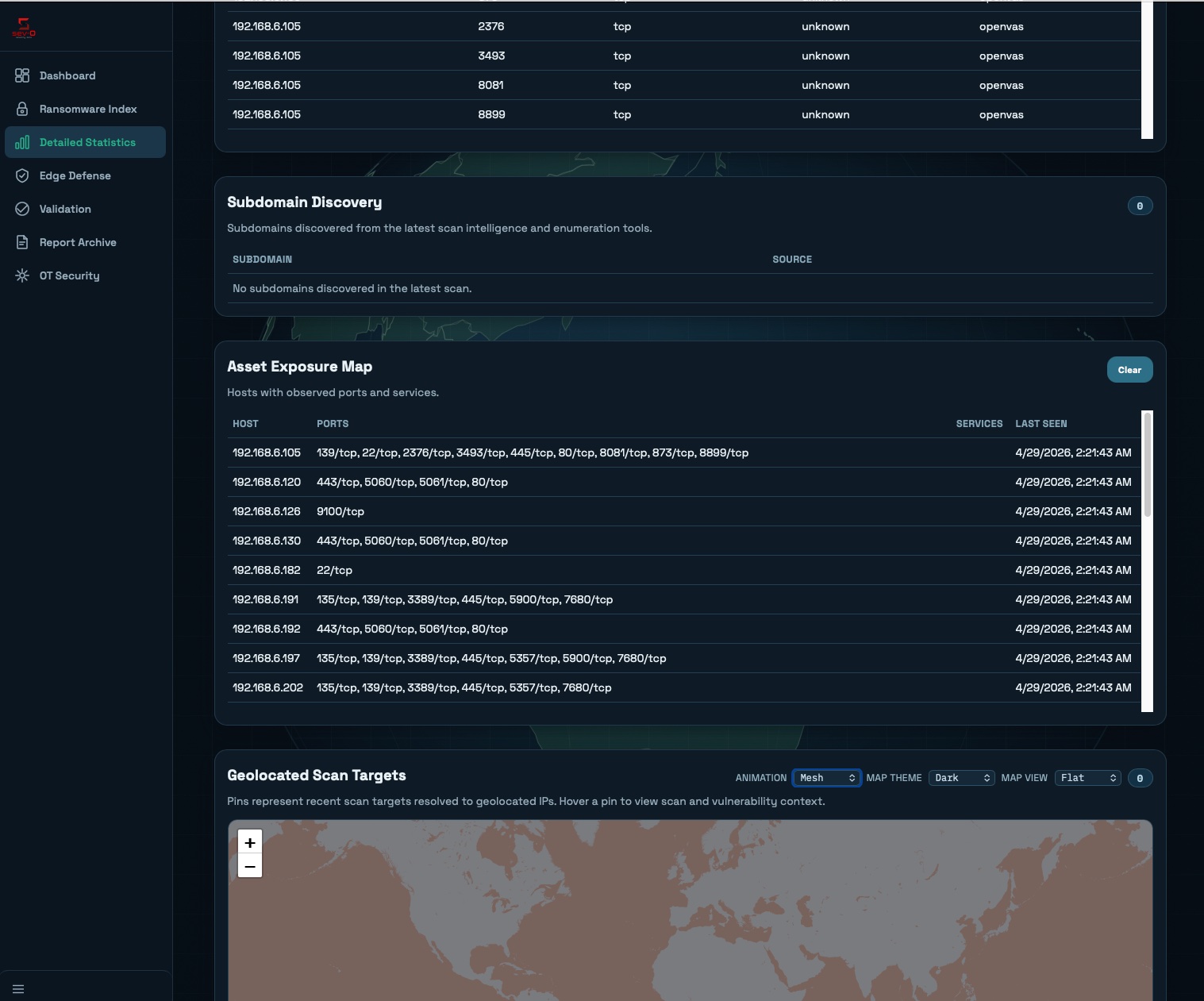
See Everything.
Multi-engine scanning orchestrated across seven scan modes. Edge agents reach networks behind firewalls over double-encrypted tunnels with zero inbound ports.
Prioritize What Matters.
EPSS exploitation probability, CISA KEV correlation, and a weighted Ransomware Exposure Index surface what attackers will actually use. Fingerprint deduplication, lifecycle tracking, and auto-close on retest kill the noise.
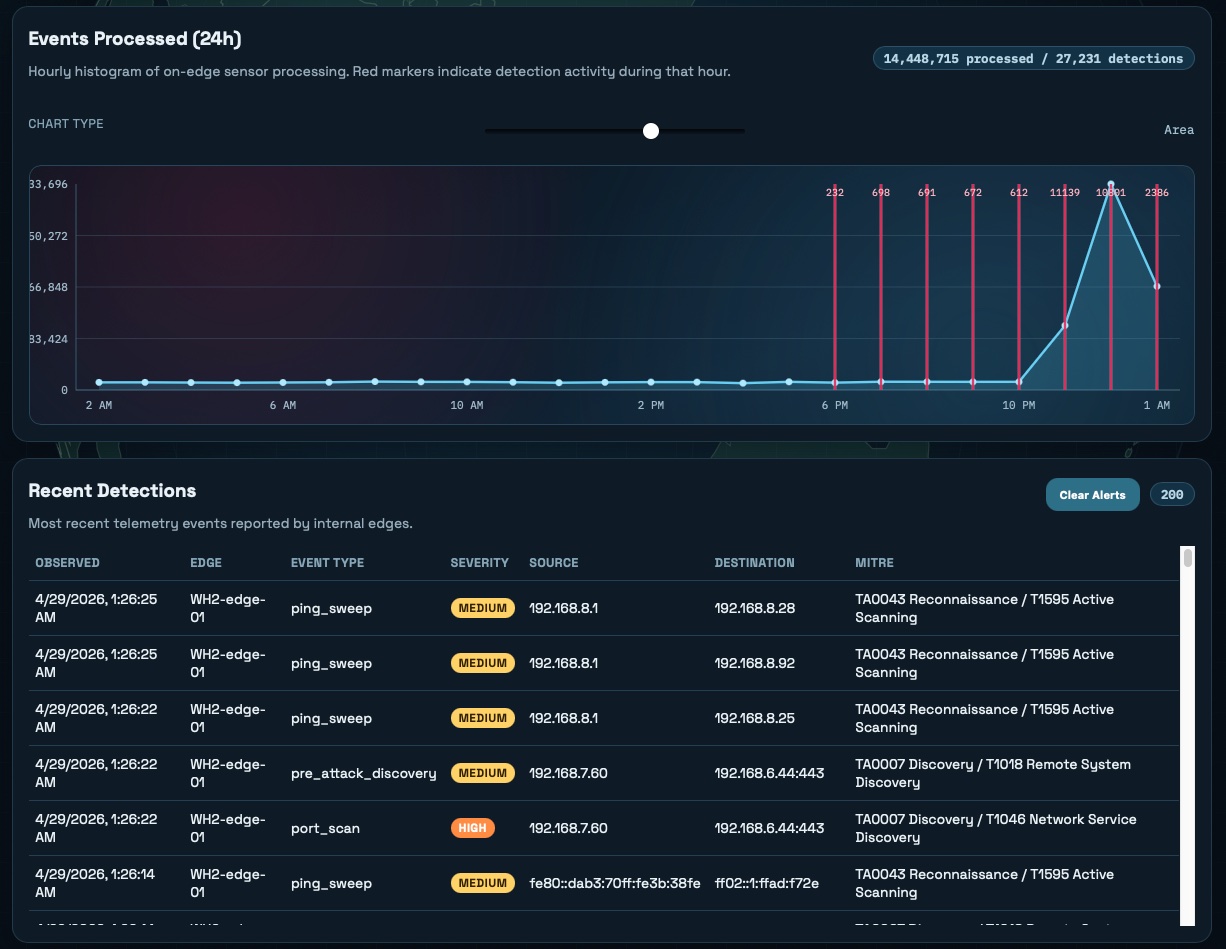
Catch Them Early.
Edge Defense turns the scanner into a sensor — passive honeypot-like telemetry detects ping sweeps, port scans, Responder behavior, and IPv6 RA anomalies before the breach. Pre-attack discovery, mapped to MITRE ATT&CK.
Prove Your Posture.
Pentest readiness scoring, executive PDFs, evidence packs, SBOMs (CycloneDX 1.5), and built-in PTaaS workflow with an 8-stage engagement lifecycle — so audit, board, and customer questions all get answered the same week they're asked.
What your team actually sees.
Built for defenders who are tired of scanner output that reads like a phone book and reports that arrive after the breach.

Built different, on purpose.
Most platforms treat industrial systems as an afterthought. We probe 11 ICS protocols safely and map every finding to IEC 62443, NERC CIP, and NIST 800-82.
EPSS plus CISA KEV plus ransomware-group association — we score what attackers will actually weaponize, not what looks scary in a spreadsheet.
The same edge agent that reaches private networks also runs as a passive honeypot, catching reconnaissance before exploitation.
The team behind SeverityZero spent 20+ years on both sides — breaching networks and defending them. That perspective shapes every score, every detection, every workflow.
Built-in 8-stage pentest workflow with client-visible status. Readiness scoring tells you when to book — not after a wasted engagement.
Nothing to stand up, nothing to patch. Optional Internal Edge Scanner drops in as a single-command Docker agent — encrypted tunnel out, no inbound ports.
Stop reacting.
Start hunting exposure.
Book a platform walkthrough — see your real attack surface in under an hour.
